Alerts & Notifications actions
Alerts & Notifications actions
Alerts & Notifications actions let you automatically send alerts to yourself or your team whenever Policy Rule conditions are met. You can learn how to create alerts and notifications actions with this article.
Prerequisites
- Appropriate role permissions to add and manage actions. By default, this is an Admin in Sightline.
- An integration with Slack. See our Slack integration guide for more information.
- If you want to send custom data, you need existing custom parameters first. See Set custom parameters for more information.
Create an alerts or notifications action
- Navigate to Sightline Cyberfraud Defense > Settings > Mitigation > Custom Action Settings.
- Under the Alerts & Notifications section, click the integration you want to create an action for.
- Click + Add Action.
- Complete the following fields:
- Action name: The name of the action and how it will appear in your HUMAN account.
- Cooldown duration: The length of time that Sightline should wait to trigger this action each time it detects a match on the Policy Rule it’s assigned to.
- Duration unit: The unit of time for the cooldown duration.
- Integration: Select the integration you want to use.
- Application data source: The application you want to send data from. You can only select one application per action.
- Event type: The type of event you want to send alerts about.
- Click Save changes.
Your notification action has been created. Next, be sure to add it to a policy rule.
Add an alerts or notifications action to a policy rule
Once you have an alerts action, we recommend adding it to a policy rule.
Be sure your policy rule’s application and event type match the ones you chose above. Otherwise, the action won’t appear when you try to add it to the rule.
- Navigate to Sightline Cyberfraud Defense > Policies > Account Policies.
- Select a rule to edit or create a new rule. See our article for more on creating policy rules.
- From the Actions menu, click and drag Alerts & Notifications to the THEN field.
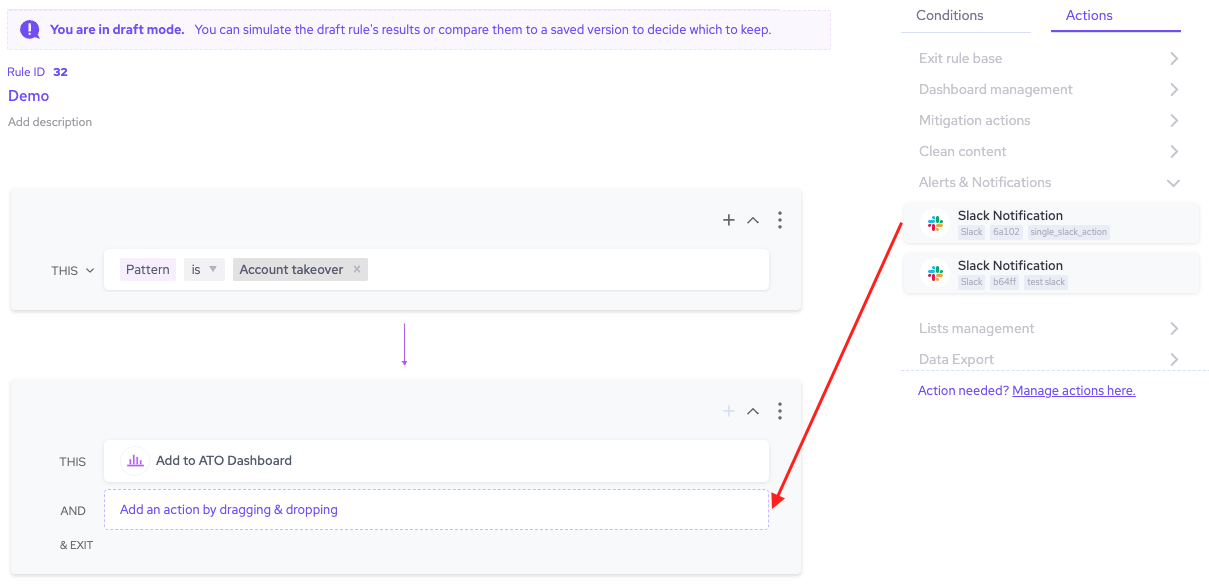
- Finish any other changes to your policy rule, then click Simulate rule.
- Click Save changes.
Now, whenever Sightline detects an attack that matches the conditions in that policy rule, it will send a notification about that attack to your chosen integration.