Investigate with the Traffic Analyzer
Once you find interesting traffic activity or want to learn more about a specific request, you can investigate using the Traffic Analyzer. The Traffic Analyzer has powerful search and filtering tools that let you scrutinize Sightline traffic and help you learn more about bot activity on your applications.
You can access the Traffic Analyzer from Sightline Cyberfraud Defense > Investigate > Traffic Analyzer. You can learn about typical use cases for the Traffic Analyzer in this article.
While this article covers common examples, these are not the only situations where you can use the Traffic Analyzer. It is a flexible tool meant to enable your team’s investigation, exploration, and understanding into your activity. We recommend experimenting with the search and filtering tools to find results that interest you.
Prerequisites
- If you want to filter on specific custom parameters, then you’ll need to set them up first.
- If you want to frequently export data from the Activity Timeline, then we recommend setting up data export instead.
Investigate traffic spikes
If you ever notice a spike in your bot traffic in the Traffic Overview, you may want to learn more about what happened during that time. This might include where that traffic came from, what paths it was active on, or other characteristics about it. If that’s the case, then you can follow these general steps to start your investigation.
If you’re investigating blocked traffic, we recommend investigating with the Sightline Threat Tracker. This dashboard automatically groups bot traffic into different Attack Profiles and directly compares forensics to legitimate activity.
1. Apply filters
After you find traffic you want to investigate in the Traffic Analyzer, navigate to Sightline Cyberfraud Defense > Investigate > Traffic Analyzer and apply the same filters there. This is to ensure you’re investigating the right period of traffic.
![]()
2. Isolate interesting traffic
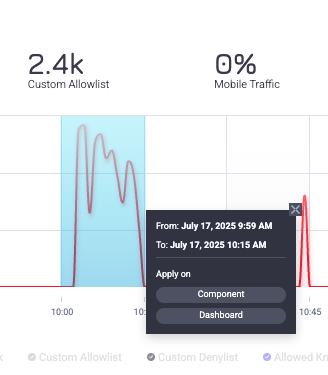
Once you have the right period of traffic, you can click and drag over the spike in the Traffic Over Time graph like in the example below. You can choose to hone in on this traffic in either the Traffic Over Time component or on the entire dashboard. We recommend applying it to the entire dashboard if you want to learn more about just that spike.
You may need to zoom in on the spike multiple times to isolate the traffic that interests you.
3. Assess traffic characteristics
Now that you’ve isolated the traffic you want to investigate, you can use the available Analyzer components to learn more. For example, you might look at the Top Countries component to find any countries you wouldn’t expect in the distribution. If there’s an unusual country with a high amount of traffic during that time period, that might indicate that there was suspicious activity at that time.
You could also consider the Top Paths component, which lists the most frequently visited paths during the time period. If there’s higher than usual traffic on sensitive routes, then that might indicate that malicious activity occurred and they were attempting to access sensitive information on your application. Or, if there’s new paths that you typically wouldn’t expect appearing on this list, that may indicate bot activity as well, since you wouldn’t expect legitimate users to frequently visit those paths.
It may also be useful to see each individual request during that time period. This can help confirm why each request was labeled as bot activity. You can view individual forensics for each request in this traffic from the Activity Timeline, which logs data for up to 60,000 requests. You can also export ![]() this list.
this list.
Takeaway
There are a variety of components that you can explore. You can get more details for each one in About the Traffic Analyzer. Be sure to take advantage of all the data available. Typically, one component is not enough to draw conclusions.
Investigate specific identifiers
Sometimes, you may want to learn more about a specific identifier. This may be a block ID, an IP address, or a specific path. In that case, the Traffic Analyzer can isolate that identifier and expose its characteristics so you can learn more about it.
1. Search for the identifier
To get started, we recommend searching ![]() for your identifier. This will display all traffic and insights for that identifier. For example, you can look for a specific block ID. HUMAN assigns a unique block ID to sessions it blocks. You can use these IDs for further reporting or troubleshooting if needed.
for your identifier. This will display all traffic and insights for that identifier. For example, you can look for a specific block ID. HUMAN assigns a unique block ID to sessions it blocks. You can use these IDs for further reporting or troubleshooting if needed.
2. Apply filters
Next, be sure that the filters applied to the Analyzer match the time period, application, and other information you want to investigate.
![]()
3. Assess traffic characteristics
Now that the dashboard’s updated with the proper data, you can start assessing the various components available to learn more about your identifier. For example, you might start with the Traffic Over Time graph to see associated traffic with a block ID. This can help determine when it was active and, in particular, when it was blocked or allowed. If it was blocked, you can review overall traffic at that time to determine if it makes sense that this ID was blocked or not.
Another option is viewing the Top Paths that were visited during this traffic. These paths can tell you where the traffic was most active. If this was malicious traffic, you might observe an unusual volume of traffic on a particular path, or you may notice sensitive paths were visited more frequently.
It may also be useful to see each individual request during that time period. This can help confirm why each request was labeled as bot activity. You can view individual forensics for each request in this traffic from the Activity Timeline, which logs data for up to 60,000 requests. You can also export ![]() this list.
this list.
Takeaway
There are a variety of components that you can explore. You can get more details for each one in About the Traffic Analyzer. Be sure to take advantage of all the data available. Typically, one component is not enough to draw conclusions.